Since the product is no longer sold on Amazon, I am left with putting this product review here. I got a bunch of GE smart toggle switches back in 2016 and installed them in various smarthome builds. Then, just yesterday (2021-03-14), I was (ironically?) installing a different smart switch on the same circuit. I turned the breaker on and off a handful of times while installing/testing the new one. And then I heard a clicking. Click… click…click… click… click… like a metronome with 1 second delay. It was the GE 12727 smart toggle from 2016. It was just clicking and clicking and clicking. At first I thought for sure the new switch was interfering with it somehow so I disconnected it and the clicking continued.
I guess a 5-year life isn’t terrible, and that one of the issues of going all in on home automation is that complexity generally leads to lower reliability. I can handle replacing the ones in my home, temporarily with the OG dumb switches and then with new upgrades (I’ve been using Inovelli switches recently based in Michigan what what!, which have cool extra features). It’s a lot more problematic when something like this happens at my mom’s house and she has to like call an electrician.
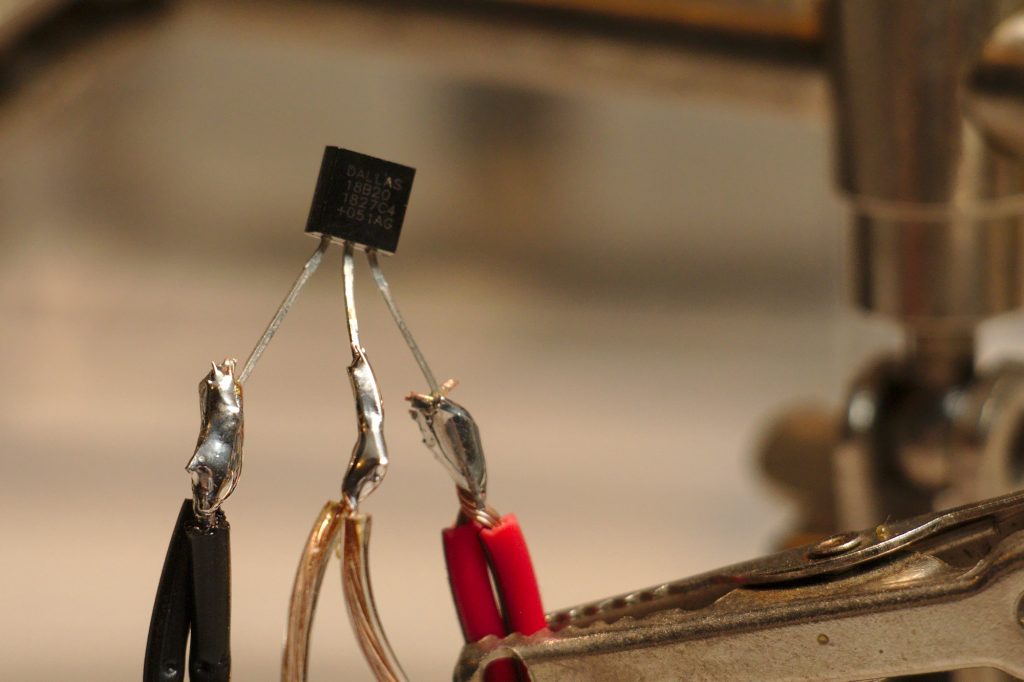
Apparently people have found that this can be fixed by changing out a capacitor.
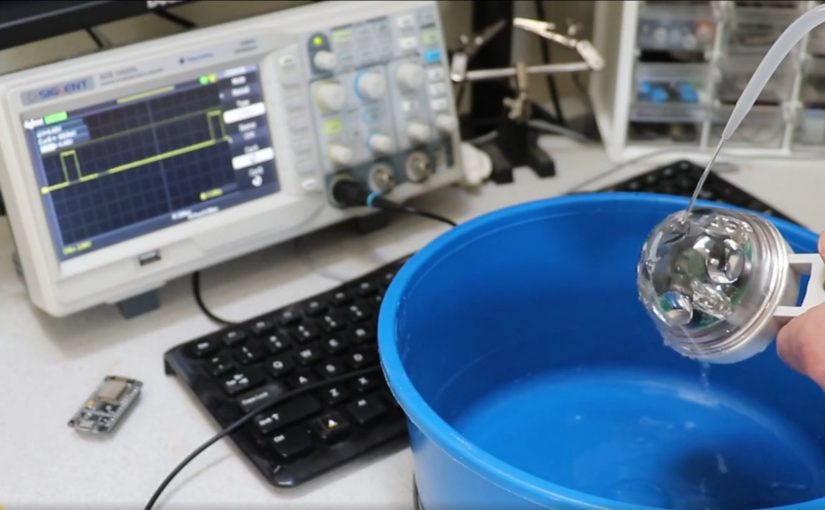
And here’s a video of a similar fix. I’ll try it out and report back.