If you have a digital video recorder (DVR) hooked up to some cameras and you want to access it remotely when something happens, you can set up remote access to review things from wherever. Here’s how to do it.
In my setup, there’s a public-access wifi router near the security cameras and a cable to this router from the security closet. I replaced the original router with one capable of running OpenWRT and then setup a VPN to allow remote access and then put the security cameras on an isolated VLAN so the normal wifi users (i.e. every resident in the building) don’t have access to the DVR. Sure the DVR has accounts too but it can’t do HTTPS without having all users install root certificates and I don’t want people sniffing the quasi-public wifi for DVR passwords.
OpenWRT flash and setup
I got a Linksys WRT 1900AC router for this job, knowing that I’d want some good CPU for sending live video over the VPN. This one seemed pretty good and was supported by LEDE/OpenWRT (they’re re-merging) with open-source radios and everything. I got one and flashed it with no big troubles. I set up the wifi.
VPN server setup
I’ve set OpenVPN up on lots of routers and am getting good at it. With LEDE/OpenVPN you basically just follow these instructions. I also like to harden things a bit by limiting the ciphers to secure ones and using a pre-shared secret. Once your server is up, generate keys for each remote user.
VLAN setup
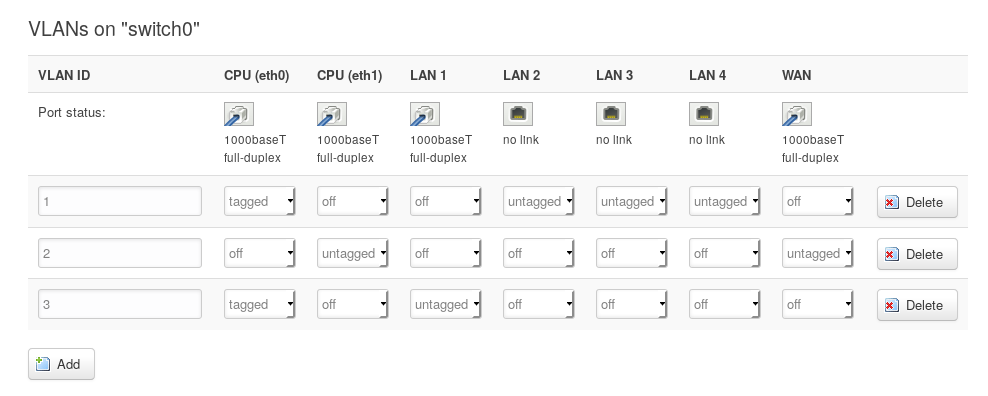
Setting up the VLAN was fairly easy once I figured it all out. First you go into the Switch configuration and add a new VLAN ID. The word “tagged” is defined in IEEE 802.1Q and just means “will communicate with other VLANs” so we set the eth0 one on the LAN and VLAN both to tagged so they can route to one another. In this example I have turned LAN port 1 into a totally new isolated VLAN. Exciting.
 Then you go to Interfaces and make a new one for the VLAN, setting its physical setting to link to the new VLAN device created in the previous step: eth0.3.
Then you go to Interfaces and make a new one for the VLAN, setting its physical setting to link to the new VLAN device created in the previous step: eth0.3.
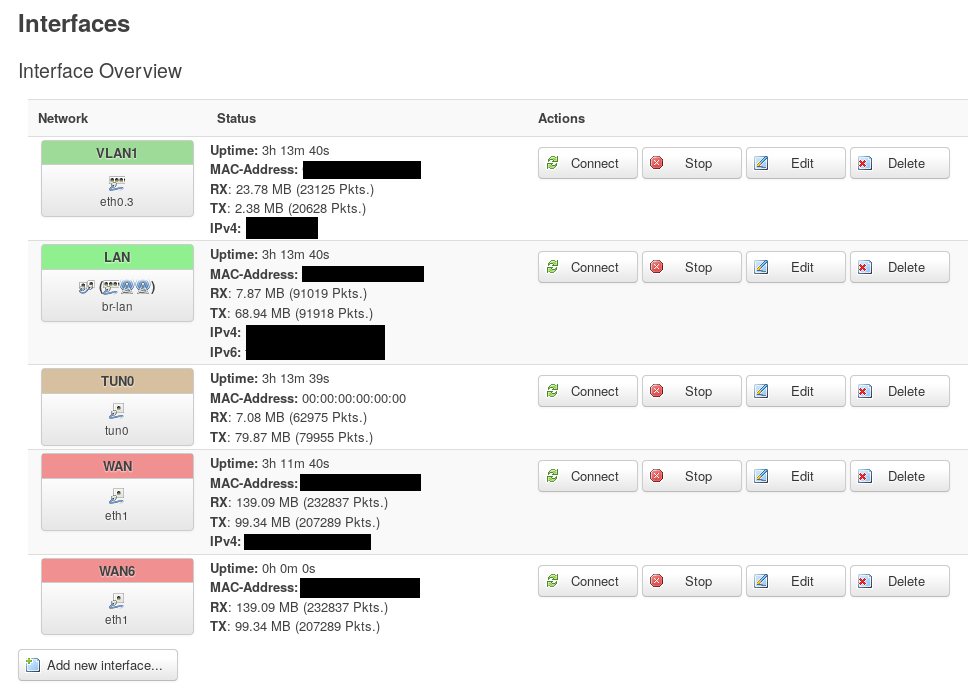
Edit the interface and give it a static address on the new subnet you want to create (e.g. 10.1.0.1). Then turn on the DHCP server if you want it to dish out ip addresses to things plugged into it (they will become 10.1.0.2, etc.).
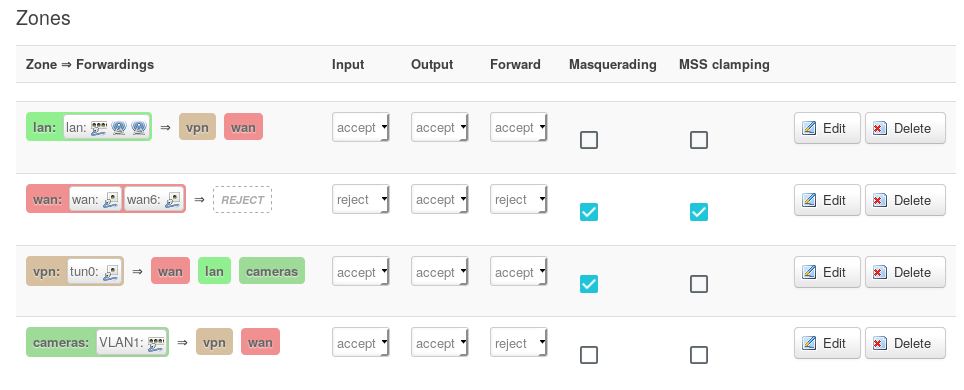
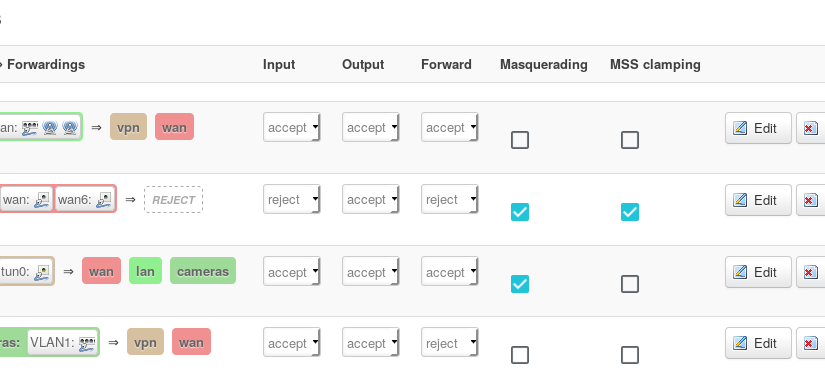
Now you just have to set up the firewall. Go to firewall and create a new zone for your VLAN. I called mine “cameras” and only allowed it to communicate with the VPN and the WAN. I could have just had it do VPN in my case, and your application may have different needs. Again I did this just so the LAN users chilling in the lobby couldn’t try to hack the DVR.
Client setup
With a linux client, it’s easy to connect using openvpn package and the network manager openvpn extension. Since my HOA board will probably mostly use Windows, I had to scrounge around to find a Windows PC to test on. It was fairly easy to install the openvpn client. I just pasted the config file and keys into the config directory on that machine and then right-clicked openvpn in the tray and the connection showed up. I had to start openvpn client as admin by right-clicking it a few times before it actually worked.
Then to access the DVR, the manufacturer had a chrome extension that works in linux and windows so that was kind of nice. You an also get a phone app.
Last steps
Back up your router config at this point in case someone resets your router.
Fabulous! Sadly, I get confused as my OpenVPN server is on my home Ubuntu server not on my OpenWRT router. So I am unsure on how to do this as I sort of understand it. Again thanks for this as I learned a lot from it.