So with all the recent revelations about everyone spying on everyone, I decided to look into what it would take to get fairly secure communications capabilities so my stuff wasn’t just in the open. I became a cryptography dilettante, and it is pretty fun. I have explained what I’ve learned to a few people so I figured I’d just write it all down here. It’s surprisingly easy and free to do.
Writing secure emails or transferring files securely
One basic thing you should be able to do securely is to send an email or file to someone that only they can open. To do this, you can use a free technology called Pretty Good Privacy, or PGP. Some nice free software that uses this is called the Gnu Privacy Guard. Go to GnuPG.org and download the relevant files. If you’re on Windows, get gpg4win (be sure to install GPA when it asks), Mac users can use GPGTools, and Linux users can just get GPG and GPA (Gnu Privacy Assistant) from the repos. Step 1 now is to generate your public/private key pair. These are basically just really large numbers that are intimately tied together in a way that if someone encrypts an email or file against your public key (which you will give to them), then only he/she who possesses the private key can decrypt it. So you publish your public key far and wide (here’s mine) and keep your private key very secret and safe (and backed up on a USB stored in your safe). Anyway, just go into the GPA program and click Keys->New Key. This will generate your keypair. Protect your private key with a strong password (10+ characters, no dictionary words. And don’t do capital letter + lower case letters + numbers + symbols in that order. Everyone does that!)
Now that you have a keypair, just right click it and say export key. This will export your public key to a file. Email the file or publish it online or whatever to anyone and everyone. When they send you an email or file, they will encrypt to this public key. Meanwhile, have your friends do the same and then import their keys that they send to you (keys->import key).
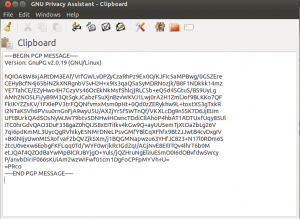
To actually encrypt, just go to Windows->clipboard and type some juicy secret. Then click encrypt and choose who you want to encrypt it to. Finally, just email them the ciphertext. It’s best to use a text-mode email by the way, so do that (it’s an option in gmail, etc.). They will get it and they can copy and paste it into their GPA and click decrypt, enter their secret password (which unlocks their private key), and they’re off. Phenomenal. Files can go the same way, just choose window->file manager instead of clipboard.
Alright! Super easy. If you use Thunderbird to read your email, you can use the Enigmail plugin that seamlessly encrypts for you. Nice! If you want a web-based email account that has tightly integrated PGP and no ads, try out hushmail.
There are a bunch of other cool things you can do with PGP like electronically sign your messages. This is something that you put at the end of an unencrypted (or encrypted) message that someone can “verify” against your public key. If no one has tampered with the message and you wrote it, then this verification proves that it was you who wrote the message. So cool.
Chatting and browsing the web anonymously and securely
So, great. Now, what if you’d like to chat with someone online and not have it be read? That’s your right. One pretty easy way to do it is through something called cryptocat. This is a Firefox extension that allows you to very easily have fairly secure chats. You COULD just click the link and install it, but you should really use The Onion Router too, which anonymizes your web traffic as well. That way, whatever you do online cannot be traced back to you because it hops through a secure set of encrypted layers on different volunteer servers first. So, FIRST go to https://www.torproject.org/ and install Tor and the Tor browser (there’s an android version too!). Then, open up the Tor Browser (which will automatically connect you to the Tor network), and then go to cryptocat and install the extension. Now you can open up a chat room and have a nice time chatting securely and anonymously. Excellent! You can use the Tor browser for anything else too.
Besides using Tor, you might want to stop using Google for many things. I started using DuckDuckGo, which doesn’t save your search history for hackers or rouge employees (or anyone else) to steal later. It’s not as good as google really, but it’s the principle that counts.
Security on your phone
If you have an Android phone, you can get these three cool apps that help with security. First is TextSecure, which allows you to exchange encrypted texts with anyone else who has TextSecure. It also stores your texts on your phone in an encrypted database, so if you lose your phone, no one’s reading your stuff. The same company makes RedPhone, which allows you to speak with anyone securely who has RedPhone. That’s totally sweet. I will admit that the voice quality in the case I used it in so far was mediocre. Finally, there’s Orbot, which is Tor for your phone, anonymizing your web traffic. Fun times.
Securely store files
If you want to keep a USB stick or a part of your hard drive that is encrypted (in case it gets stolen or something), the TrueCrypt tool is fantastic. It can even make a Hidden volume, where if you type a dummy password, dummy files show up but if you type the real password, the real files show up. And no one can prove the real files exist. That gives you what’s known as plausible deniability, a term coined by the CIA.
Encrypting with Truecrypt is different than with PGP because to send the file, the recipient would need to know the password. But how can you send the password securely? With PGP. So might as well just use PGP for the whole transfer.
If you’re a friend of mine who wants to try any of these technologies out with someone, just drop me a line and I’ll play along. I got a lot of this info from a reddit AMA, which you can read here.
Privacy is important, even if you have nothing to hide. Ok have a nice day!
Update: There’s a great collection of related information at this page.
Unfortunately, I think your advice will be less useful for a layman than what you had hoped. Here’s the functional instructions you gave for the software.
“Anyway, just go into the GPA program and click Keys->New Key.”
“To actually encrypt, just go to Windows->clipboard and type some juicy secret. ”
See, the problem is that anyone who needs the advice will be using gpg4win (or the Mac version) and not the GPA that your instructions are for. That means that anyone with Windows will be using Kleopatra for this, which is software rarely mentioned in these tutorials.
It also sucks that the program doesn’t have any clipboard. I see potential problems as a result involving file types. I can encrypt a text file, but then how will the person who receives it know that the data should be a text file? If they were expecting plain text, it seems to me that the process would give some nonsense data. Maybe this isn’t a concern with the way that GPA operates, but it’s clearly an unanswered question for someone who just opens up the program wanting to try it.
I’ve also shot myself in the foot in efforts to convince colleges to try encryption by sharing articles about how the intelligence agencies will flag encrypted communications as being suspicious. With almost all major providers of email and other services you aren’t allowed to send and store encrypted files. By all means, you can circumvent this by using ASCII, but in doing so, you knowingly violate the spirit of the restriction. For years I’ve been seeing the writing on the wall that random data is at risk of being criminalized through the advent of cloud services. If you can’t identify a number, then you can’t say for sure that it’s not an illegal number. The hazard that we’ve been blind to for so many years is that 99.99% of our communications are automatically parse-able, making non-compliant data forms clear as day to any analysis algorithms. What ads would gmail display in response to seeing random data being sent? It’s a nonsense question. Their algorithms understand everything you write, and when it doesn’t, that logically goes to an “unknown and suspicious” bin. Even now almost no one gets the obviousness of this chilling effect.
Not so! GPA comes with gpg4win these days bro. I made the instructions in Windows and verified them on Linux. Haven’t actually tried on Mac yet. If your friends are worried about all encrypted data being criminalized then they had better stop using online banking or shopping online too!